Audit Logs: Be Ready When Activity Is Questioned
When access or system changes are questioned, pulling logs from multiple tools slows everything down. Audit Logs centralize cross-system activity tied to real work. Confirm what happened without chasing evidence.






When questions arise, logs are scattered
Access records and system changes sit across multiple tools. When someone asks what happened, teams scramble to gather logs manually. That delay increases compliance risk and slows down response time.
Keep logs in one place and ready
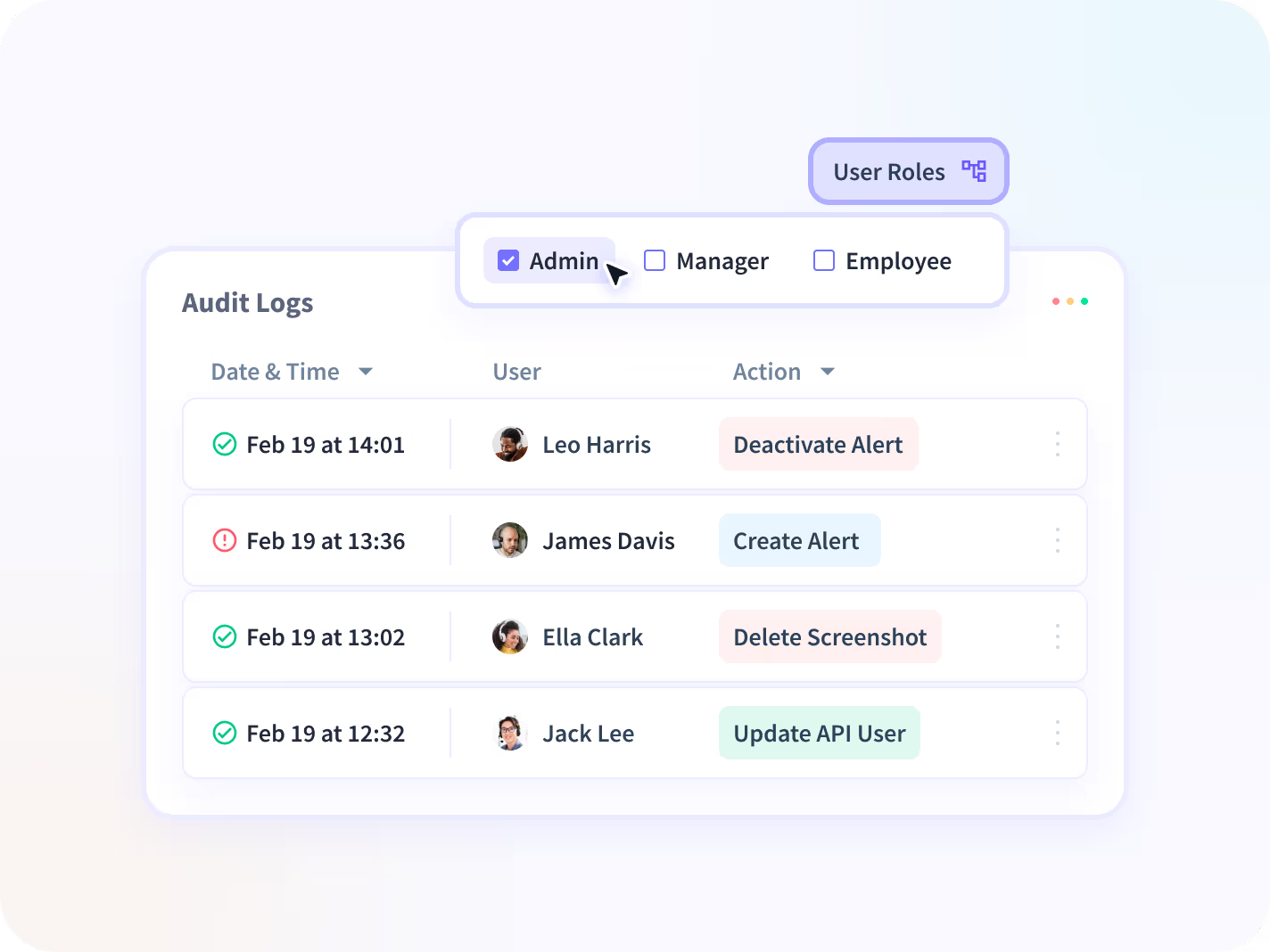
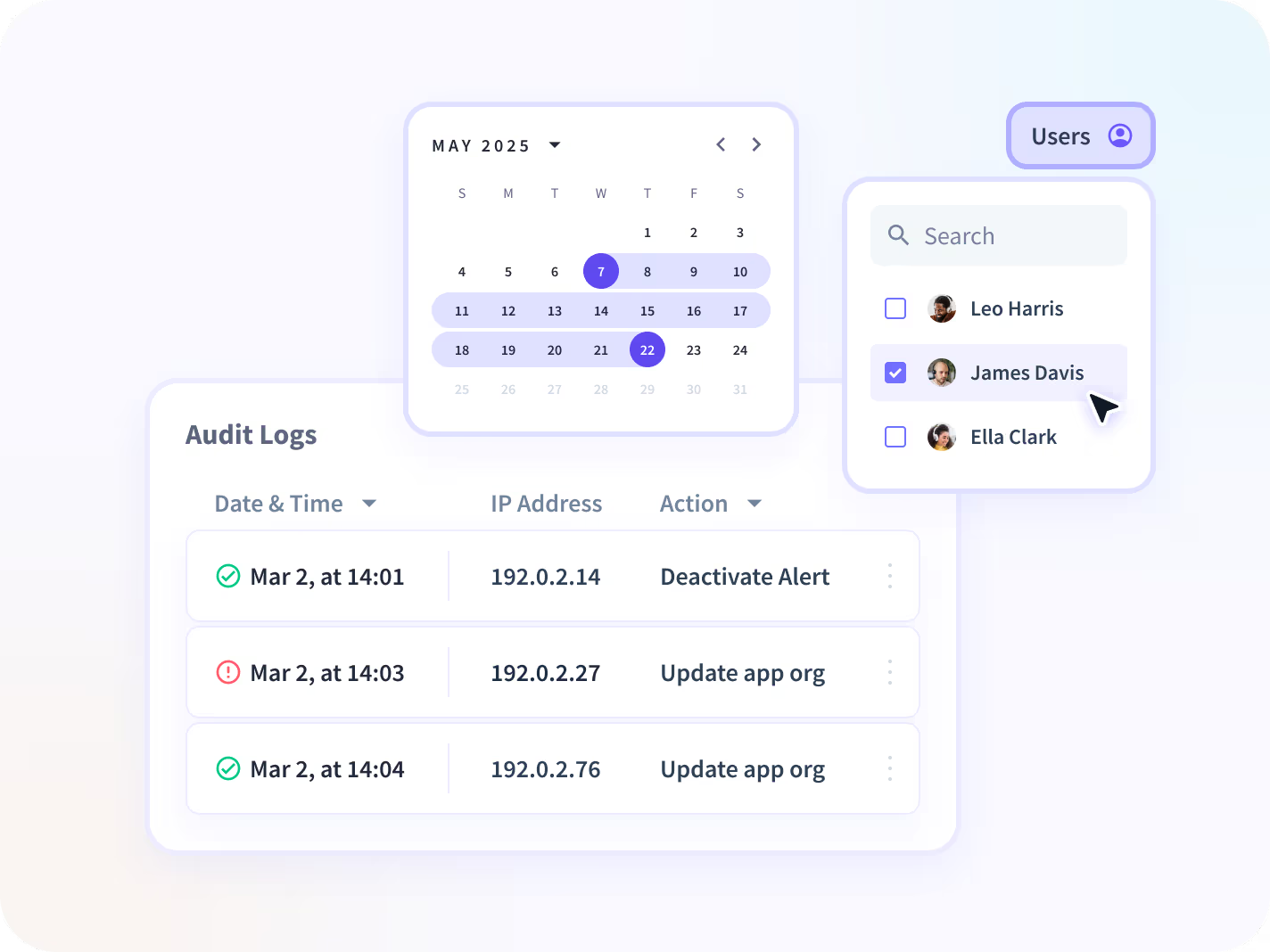
Audit Logs connect access records, system changes, and application activity into one cross-system view tied to real work. Review documented actions quickly without stitching logs together.

Complete Activity Records
Access and change history in context.
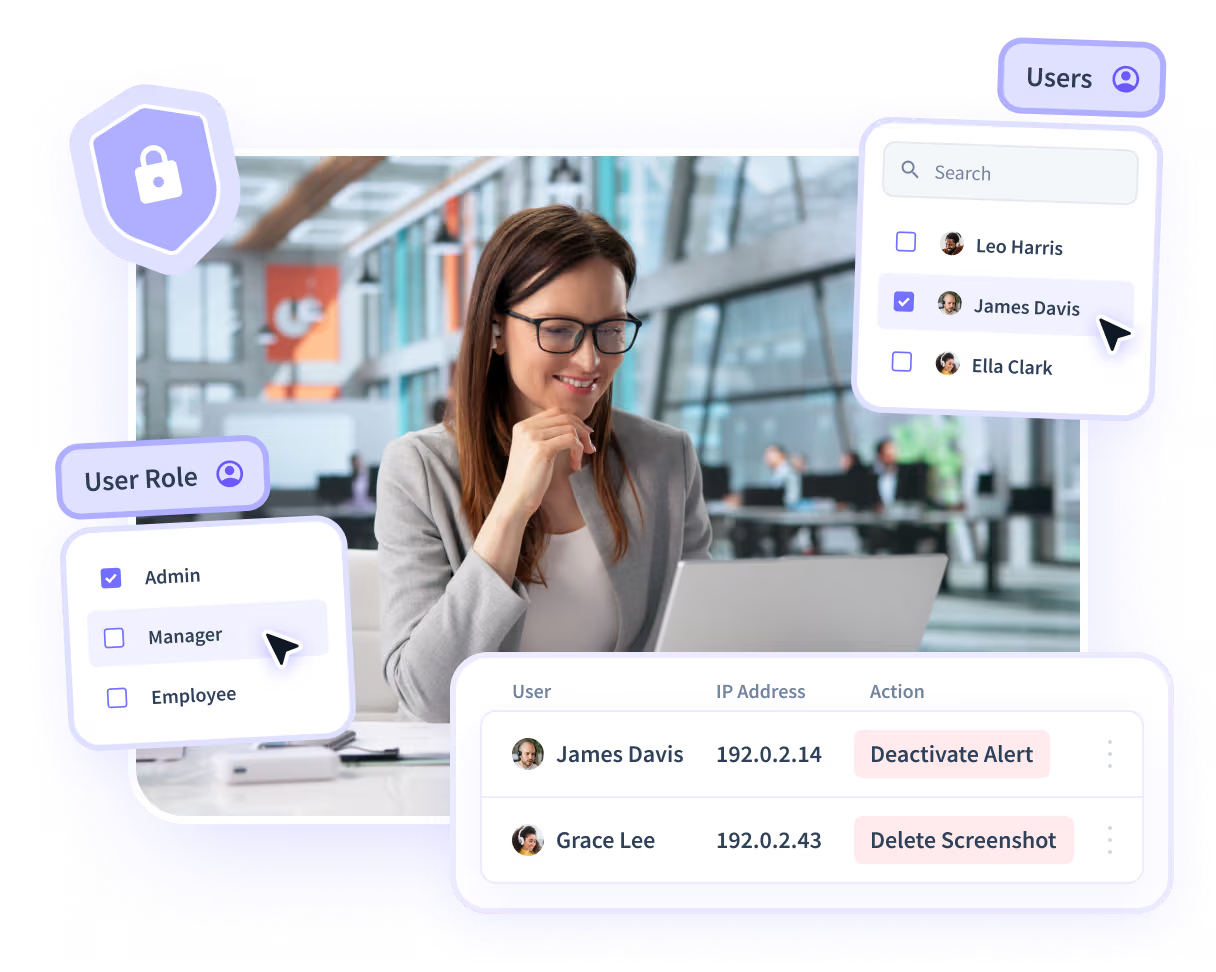
Centralized Log Access
Cross-system activity in one record.
Search &
Filtering
Find actions by time, user, or event.
Retention & History
Preserve logs for audits and reviews.
Export & Reporting
Generate audit-ready documentation.
Use cases
Insightful seamlessly integrates with your technology ecosystem
With over 50 integrations available on the Insightful platform, connecting with your team's top tools is just a click away.
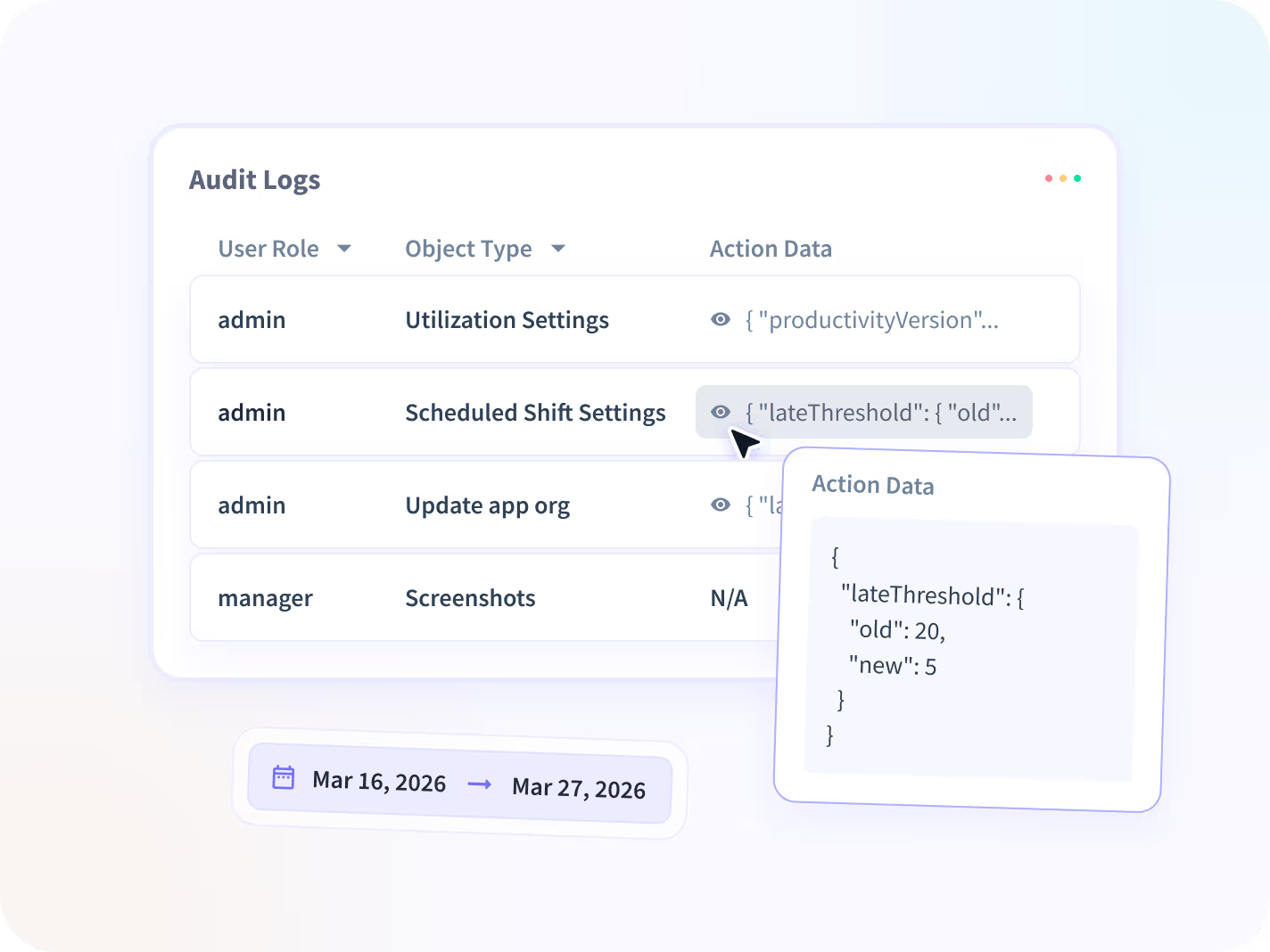
Build a defensible record
FAQs
Most systems generate their own logs, but they remain isolated within each tool. Audit Logs connect cross-system activity tied to real work into one documented record.
Instead of switching between platforms, teams can review actions in sequence and respond to compliance or review requests without manually stitching evidence together.
No. Traditional audit log monitoring focuses on storing or reviewing system-level events within individual platforms.
Audit Logs consolidate access records, system changes, and application activity across tools into a unified, defensible record. The goal is not monitoring for its own sake, but making it possible to confirm what happened when activity is questioned.
Audit Logs are used when leaders need verified documentation of activity across systems. Common triggers include compliance reviews, internal audits, executive questions about access or changes, and early-stage security investigations.
They ensure teams are prepared before issues escalate.
Audit Logs provide a documented history of access and system changes across tools. When auditors request evidence, teams can generate a clear record of who did what and when, without pulling logs from multiple systems.
This reduces response time and lowers compliance exposure.
Audit Logs provide a cross-system documentation layer that keeps activity organized and review-ready.
Forensics is used after a defined incident to reconstruct a detailed, time-aligned investigative timeline. Audit Logs ensure the records exist and are accessible; Forensics enables deeper incident analysis when required.
.svg)

























